Open VM Tools is now supported with NSX Distributed Firewall
Although a recurrent request, the use of Open VM Tools on guest or workload virtual machines has never been validated with NSX Distributed Firewall. It got quite unnoticed, but a small sentence in the NSX for vSphere 6.3.2 Release Notes changed the game:
**Starting in NSX 6.3.2, Open VM Tools is supported with Distributed Firewall.**
In NSX, VMware Tools are required to translate vCenter objects into IP. Indeed, the underlying NSX distributed firewall rules configured within the kernel are IP-based, despite being abstracted as objects at the configuration layer so it is a requirement to run VMware tools in all virtual machines so their addresses are reported into vCenter. Until now, Open VM Tools were never validated by engineering: it didn’t mean that it was not working but that you could potentially face issues as VM to IP mapping may not correctly occur.
Note: 2 additional IP detection types are also available (on a cluster-basis): DHCP snooping and ARP snooping.
Little reminder: what is Open VM Tools (OVT) again? :)
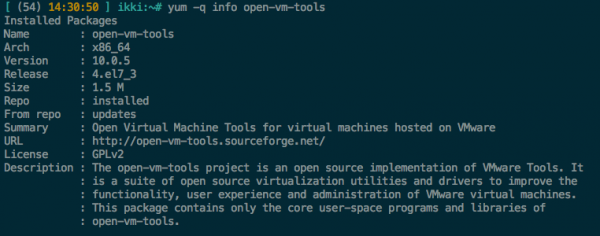
The Open VM Tools (or OVT, also often referred as open-vm-tools) is an open source implementation of VMware Tools. Its primary purpose is to enable operating system vendors and/or communities and virtual appliance vendors to bundle VMware Tools into their product releases. You can use them to replace the VMware Tools quite easily, either with rpm packages or with YUM / APT.
At the time of this writing, open-vm-tools are available with these operating systems:
-
Fedora 19 and later releases
-
Debian 7.x and later releases
-
openSUSE 11.x and later releases
-
Recent Ubuntu releases (12.04 LTS, 13.10 and later)
-
Red Hat Enterprise Linux 7.0 and later releases
-
CentOS 7.0 and later releases
-
Oracle Linux 7.0 and later releases
-
SUSE Linux Enterprise 11 SP4, 12 and later releases
More to read: